As some of you already know, I’ve recently become a free agent and have begun the search for my next great job. I’ve learned a lot about the “brave new world” of job hunting over the last couple of weeks, and to be honest it’s been a bit scary.
I’ve only had two employers over the past 18 years, and in both cases I was laid off due to staff reductions. I jokingly told my wife that someday I’d like to experience what it is like to actually quit a job, rather than having a job quit me. After leaving my role as a Sr. Business Manager with Convergys (a large contact center organization) in June of 2007, it had been 10 years since I had applied for and interviewed for a job, and I found the idea of re-writing my resume and hitting the pavement to find a new career rather daunting. In October that same year I was contacted by someone I had worked with previously who was now working in the HR department of a public school division. She explained their IT department needed some temporary help for about 3 months, and although my role when we worked together had been in Operations, she knew I had technical skills, and wanted to know if I was interested. I accepted, thinking the work would pay some bills in the short-term while I continued to tweak my resume and find full-time employment. Instead, I re-kindled my passion for hands-on technical work, and ended up accepting a permanent position in January 2008, and worked there until April of this year.
That was my first taste of social networking and finding a job.
8 years later it seems leveraging the power of social media and professional networks is the absolute best way to find that new role. The general consensus seems to be that sending your resume out electronically to a bunch of automated HR systems, or submitting your CV and cover letter through a web form is not going to get you that position you wanted. It is frightening to read articles on the subject of modern recruiting explaining how automated software scans and scores your resume and rejects it before a real human being ever reads it. How prevalent that actually is I don’t know, but I do know that when I send a resume via email, I often envision it being packed away in a warehouse and forgotten like the Ark of The Covenant in Raiders of the Lost Ark.
Decisions…decisions
I have a few decisions to make. The first and foremost seems to be deciding what I want to do next. In 1997 I began doing technical support in a call center and fast-forward 10 years later I had relocated twice, and been promoted through various roles within that same organization with experience in training, client services, project management, and operations management. I had managed multi-million dollar budgets, with staff and operations spanning multiple cities in Canada and the US. I had developed my business skills, and although each of the projects I had worked on over the years were technical in nature, I had not really been hands-on with technology in some time. I knew I wanted to get back to that.
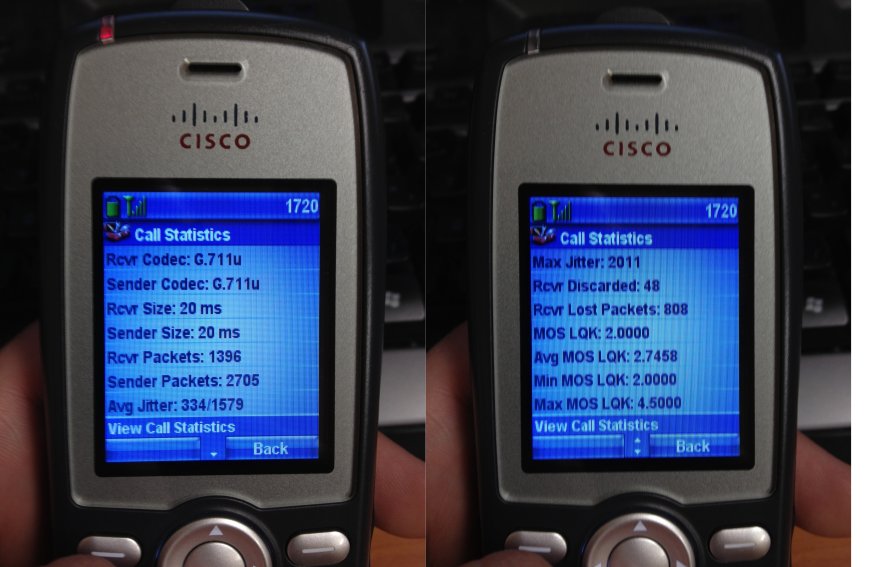
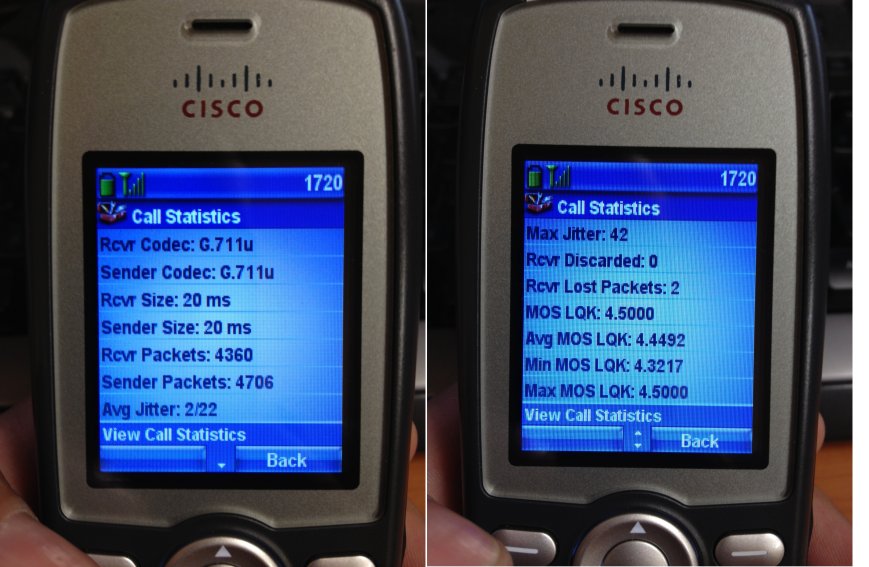
As a Systems Analyst with my most recent employer, a K-12 public school division, I had been able to spend the last 7+ years “doing IT” again. I’ve focused on networking and virtualization, and even knocked out a few certifications. The technology is what I am truly passionate about and being in a position to learn something new every day was fantastic. While it wasn’t a large infrastructure, I’ve had exposure and developed skills and experience with Cisco, HP, Dell, Microsoft, VMware, NetApp, Fortinet, and a number of other technologies. It was truly a great experience to work in a small IT shop and have access into a little bit of everything.
Somewhat parallel to this I decided to combine my business knowledge and my IT skills and started my own business 2 years ago offering managed IT services to small businesses that can’t afford their own dedicated IT staff. I’m able to partner with them and understand both the key issues that drive their business, while assisting them meet any technology needs they have. The possibility of growing the business is there, but with a family, and my wife presently on maternity leave, there is something to be said for the comfort and security of full-time employment. Mainly the steady income and benefits.
I could perhaps work for a vendor, doing pre-sales or post-sales support, and really get to know one particular technology. I could work for a reseller, which might provide exposure to a larger variety of products. Or, I could join another IT team, but if I did it would have to be a significantly larger organization. I want to experience work in a real data center, no more 2 rack switch closets with a portable AC unit that serve as one.
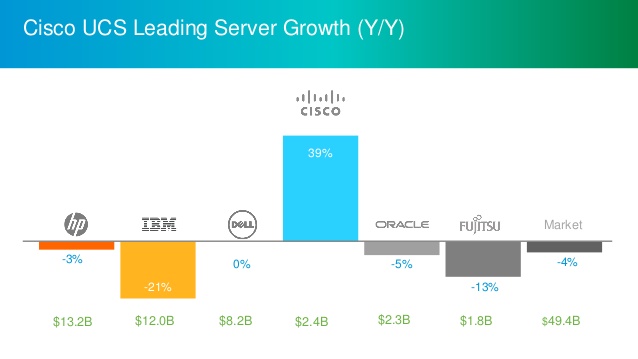
My “dream job” would probably be working somewhere with responsibility for a decent-sized VMware cluster, maybe on Cisco UCS or another converged/hyper-converged platform, and management of the underlying L2/L3 network infrastructure.
Wherever I go, I want to be able to make a real contribution and continue to develop myself as an IT professional. I want to ask dumb questions and learn from others and I want to be part of a great team.
Ongoing Learning
In my previous role there was some opportunity for on-the-job learning, but very little time or budget was set aside for real professional development. The reality is, in a public education environment, budgets seem to dwindle year after year and there is constant juggling between departments as to where the dollars are needed the most. Funding someone to take a $3000 course at Global Knowledge was out of the question.
That being said, I believe ongoing learning is critical, and found ways on my own to learn, play with, study and prepare for certifications. I’ve developed a fairly decent home lab, without raising too many red flags with my wife in terms of our household budget, and have been able to prepare for and pass a number of certifications over the last several years.
I’m in the process of wrapping up my CCNP R&S with one exam left (ROUTE), and completed the VCP5-DCV in December. I’ll likely focus on learning more about VMware’s NSX product and perhaps look at writing the VCP6-NV exam along with upgrading my VCP5-DCV to the VCP6 version.
Long term, I plan to dedicate myself to the challenge of the CCIE.
Success stories
I’ve read and been inspired by a couple of other folks in the industry who have used social media as a platform or jumping-off point to find their new career, and although I certainly don’t have the same sphere of influence these people have, I’m going to try to do the same. Hat tip to Keith Townsend for sharing his story over at VirtualizedGeek.com and also to Sean Thulin whose journey is told on his blog at Thulin’ Around and congratulations to both of them on their new roles.
Now, do I expect my dream job to simply fall into my lap? Of course not. I’ll be engaged in some of the more traditional methods of searching online and reaching out directly to a handful of contacts who may know of some unlisted positions. First of all however, I’ll need to tweak my resume to fool those pesky HR screening tools!
So, if you or someone you know are aware of an opportunity for a skilled, loyal (2 jobs in 18 years!) networking and virtualization professional, or simply would like to learn a little bit more about me, feel free to reach me here, or on Twitter or LinkedIn. I’d love to hear from you!
Otherwise feel free to share, retweet, or carrier pigeon this article and help me cast the net as far and wide as possible.